Building a Defense‑in‑Depth Auth Strategy for Public Content APIs (REST)
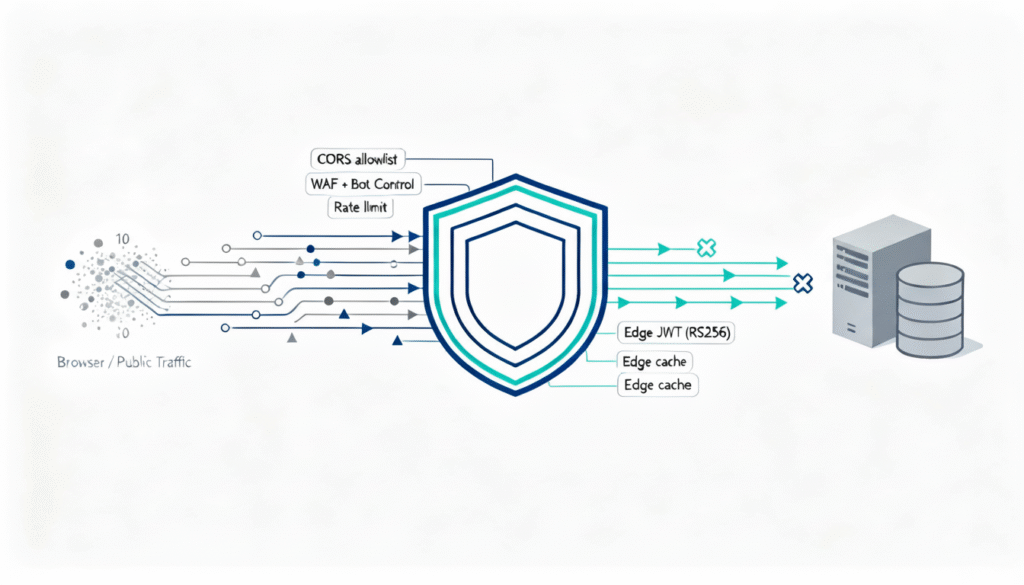
Java/Spring backend • AWS CloudFront • Apigee X • RS256 JWT with JWKS (Apigee KVM) • Optional API Keys for Partners • Explicit Origin Allowlist via CloudFront Functions TL;DR Table of Contents Why “auth” for public content APIs? “Public” does not mean “unprotected.” Ratings, reviews, and Q&A endpoints attract scraping, cloning, and sudden bursts that […]
Building a Defense‑in‑Depth Auth Strategy for Public Content APIs (REST) Read More »